
Digital Disaster – Hackers Wipe Out a Life. Everything.
They said they just wanted his three character Twitter handle, “Mat”. Here’s how the hackers got to work.
- They broke into and deleted his Google account.
- Next they took over his Twitter account.
- They tweeted racist and homophobic messages.
- Finally, they sabotaged his AppleID account and used to remotely wipe out all of the data on his iPhone, iPad, and MacBook – including the first year’s worth of photos of his little daughter.
In the space of one hour, the Wired magazine journalist’s entire digital life was destroyed. Here’s what he regrets most.
What I Regret
Had I used two-factor authentication for my Google account, it’s possible that none of this would have happened, because their ultimate goal was always to take over my Twitter account and wreak havoc… Had I been regularly backing up the data on my MacBook, I wouldn’t have had to worry about losing more than a year’s worth of photos, covering the entire lifespan of my daughter… Those security lapses are my fault, and I deeply, deeply regret them.” – Mat Honan
Protect Yourself
 If you’ve been following along with us on Digital Zen, you’d already have turned on Google’s two-factor authentication. It only takes a minute! Go the extra step and call your bank to ask if they offer security tokens, and request one if they do.
If you’ve been following along with us on Digital Zen, you’d already have turned on Google’s two-factor authentication. It only takes a minute! Go the extra step and call your bank to ask if they offer security tokens, and request one if they do.
You’d also have read about the importance of an automated, remote backup system. I use a combination of Dropbox, Gmail, and Codespaces (cloud tool for coders). Samantha uses Carbonite.
The point is, use something, and automate it.
Amazon and Apple Security Flaws Exposed
While it’s shocking that hackers were able to do this much damage in just one hour, the crime was inevitable. Major security flaws at both Amazon and Apple facilitated the hack, and both companies have taken immediate measures to tighten security. Apple confirmed a suspension of over-the-phone password resets, and Amazon will no longer allow over-the-phone confirmation of identity with just a name, email address, and mailing address – three pieces of personal data that can be easily found online, and the back-door used by the hackers.
This Only Gets Worse
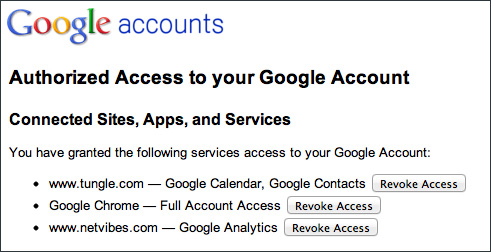
With the new era of “cloud computing” and connected devices, the higher the consequences are of any potential hack, and the more critical it is for the underlying security infrastructure to evolve along with it. This is one reason why the “one global password” concept is dangerous. Imagine if Mat had used his Google identity (or Facebook or Twitter) to subscribe to online shopping sites – and the hackers went on a fun little spree.
To see which sites you may have authorized access to your Google Account, open the Google account dashboard, click “Security” and then click “Authorizing applications and sites -> Edit”. You may be surprised at what you find.
Our hearts are really aching for Mat and his wife. Losing all those precious photos of their daughter is a huge loss. Next week, Mat will be writing “How I put the pieces of my digital life together again” and we’ll be following along and wishing him the best of luck.
Photo credit: Wired

Don't Even Think of Going Paperless Without This | Digital Zen
08/30/2012 at 4:26 pm[…] months of free backup and Samantha will earn a $10 Amazon card, which she’ll pass along to Mat Honan, if she can find […]